How to use AnuBiTux to perform crypto seizures

DISCLAIMER: This post contains some suggestions that could be helpful for law enforcement agencies or security consultants that need to seize cryptocurrencies. It aims to show how AnuBitux could be used to perform the seizure but is not intended to be exhaustive. It is also recommended to check the local law before proceeding with a cryptocurrency seizure procedure.
AnuBitux is realized to safeguard users' privacy and provide a very simple environment to manage a lot of aspects regarding cryptos. Of course, it could be used by law enforcement agencies and security consultants to perform crypto seizures.
Where?
Doing a crypto seizure, the first matter is to obtain a secure place to store cryptocurrencies With AnuBitux we can create a lot of different kinds of wallets to store coins. One of the best and cheaper ways is to store them with a paper wallet. In previous posts, we have seen some methods to realize Bitcoin and Monero paper wallets, but these procedures can be adapted also to other currencies. With AnuBitux we also can print our paper wallets without the need to connect to the Internet and download drivers, since it has a lot of them already installed.
Once we printed our paper wallet, we also need to take care of where are we going to store it. We should use a sealed container that does not reveal any information, even if exposing it near a strong light or wetting it. We also need to close it in a way that makes it difficult to open and that can reveal if someone accessed it without authorization.
If we had time to prepare the seizure we could have a hardware wallet to store the currencies we need to size. In this case, we can also use AnuBitux to manage it, because it integrates clients, drivers and udev rules for many different hardware wallets, like Ledgers, Trezors, Bitboxes, etc. In this case, it is very important to decide how to handle the mnemonic seed because, even if hardware wallets can be considered very secure, obtaining their seed could give complete control over the handled funds. If we decide to keep the seed, we can consider valid the same considerations we made for paper wallets.
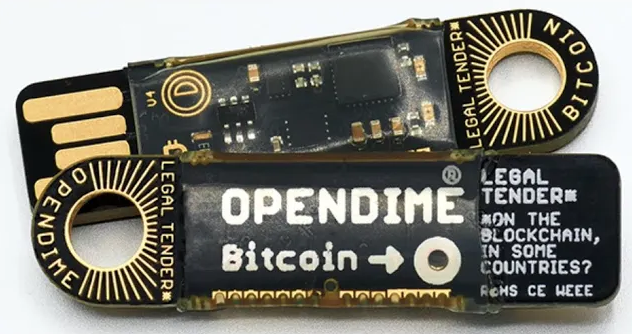
If we need to perform a Bitcoin seizure, a good way to store the seized coins could be to use an OpenDime. It is a special kind of hardware wallet, supporting only Bitcoin, that gives us a public address to send the coins to and that won't reveal the related private key unless we push a pin through the appropriate hole. So, as long as this hole is safe, we can be sure that no human has seen the private key of our address and no one could have spent the funds we sent to the OpenDime's public address.
How?
Once we have arranged something to send the coins to, we need to dispose a transaction to accomplish the seizure. We need to remember that the only way for a seizure to be effective is to have the funds on something that is under our control. So we need to be sure that there are no other copies of the wallet that is going to keep the seized coins and that there is a way to guarantee that no one can have access to private keys or seeds. So, we can't consider the funds as seized if we seize a hardware wallet, a device with some kind of wallet installed, or a recovery seed. All these things could have been backed up in a lot of creative ways so, if we don't move funds they could be accessed in many ways and our seizure could be ineffective.
Moving funds could not be that easy. There are many ways to protect cryptocurrencies from unauthorized uses, like PINs, passwords, passphrases, etc. If the owner of the funds we need to seize is cooperating, we should not encounter any problem disposing the transaction. If not so, we could need to take control of the funds against their will.
With skilled users, it could be almost impossible, but a lot of users are lazy or do not have a very strong OpSec. So we could do some of the following actions, looking for any information that could be used to take control over the funds:
- try to unlock wallet files with btcrecover, maybe using a custom password list created with credentials extracted from the users' browsers or from their devices or based on their personal information;
- scan directories for mnemonic seeds with seedsearch;
- scan directories for private keys with btckeysearch;
- try to unlock encrypted volumes and containers with veradecrypt, maybe using a custom password list created with credentials extracted from the users' browsers or from their devices or based on their personal information;
- perform an accurate house search looking for everything that seems like a mnemonic seed or a private key or any kind of wallet stuff;
- any other creative idea is welcome.
Once we obtained the information we need to dispose the transaction, we need to know how to use it. If we have found the password or the PIN to unlock a desktop wallet, we can dispose the transaction from there or we could decide to dispose it offline to avoid using the user's device. Instead, if we have found mnemonic seeds or private keys, we need to import them to a compatible client. If we don't know how the seeds were used, we can use seedcheck and try to find it out and import it to the right client. Instead, if we have found some private keys, we can refer to the procedures shown for Bitcoin and Monero.
Considerations
There are a lot of considerations that can be done when performing this kind of procedure and, as much experience we have, as many useful considerations we will be able to make.
One of the first considerations we need to make is about the network fees. A higher one could be useful to obtain faster confirmations of our transaction and consider it valid but, if the chosen fee is too high, it could impact too much on the seized amount.
When the transaction has been disposed, we also need to wait for some confirmations to avoid that someone else could make it invalid with an RBF (replace by fee) transaction, that is a transaction with a higher fee that could be processed faster and making ours look like a "double spend" attempt.
Other useful considerations could be done when dealing with multi-currency wallets, like Exodus, Coinomi, MyCellium, Guarda, Atomic, etc. First of all, it could be better to arrange a paper wallet for any of the available currencies. We also need to evaluate if the user owns tokens in his wallet that work on layer 2 blockchains, like ERC20 tokens, NFTs, etc. These tokens "live" on other blockchains and do not have their own so, to move them, we need to pay the fee with the main coin related to the blockchain on which they work. For instance, with tokens like BAT or Shiba Inu, we won't be able to move them without an amount of ETH that we will need to pay gas fees for the Ethereum network. This happens not only with tokens working on the Ethereum network but also with tokens working on networks like Solana, BSC, etc.
Final thoughts
What we have seen in this post is just a collection of tips that can be useful for those who need to seize cryptocurrencies. Of course, it is a more complex operation that needs a lot of different skills, not only regarding how cryptocurrencies work but also regarding digital forensic techniques, networking, OpSec, etc.
In this scenario, AnuBitux tries to provide a simple and safe environment that includes all the tools that could be helpful when performing such tasks.

