Hide your mnemonic seed with steganography

The ideas presented in this post and in other similar posts on this website have to be considered only like suggestions. Users should adopt the strategies that better fit their threat model and their needs.
Hiding a mnemonic seed is something about everyone has his theories but no one is able to provide the correct solution. We believe that there is no universal solution, but only a lot of different solutions that fit the needs of one user or another.
A good strategy could be to hide our mnemonic seed with steganography. For those who do not know what it is, steganography is the practice of representing a piece of information within another object in a way that could not be easily seen by others. So we could try to hide our mnemonic seed in another file, like a picture or a video. Let's see how we could do it with AnuBitux.
The procedure
To safeguard the security of this process, we kindly suggest following all these steps using AnuBitux live without connecting it to the internet and disabling all the network interfaces with the proper desktop shortcut.
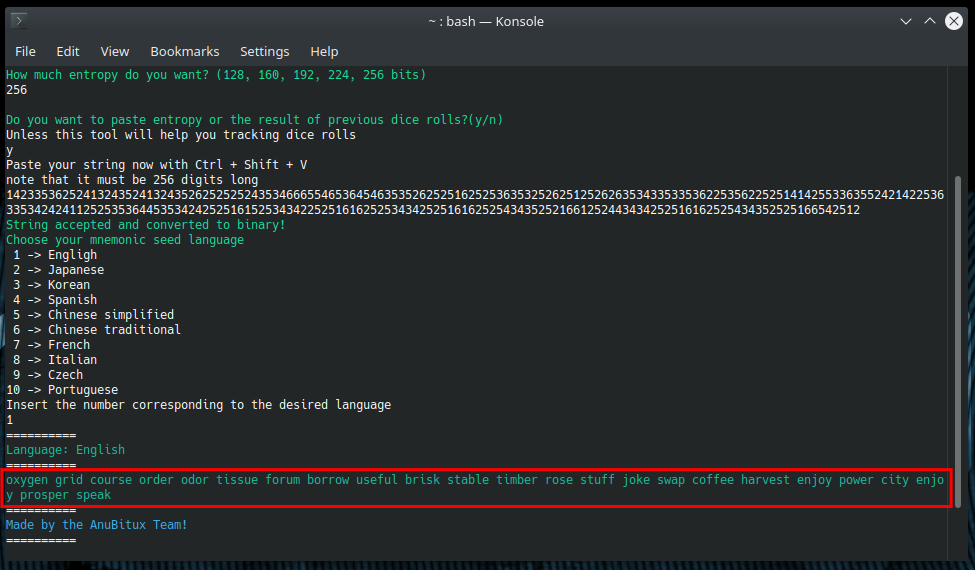
First of all, we need a mnemonic seed to hide. We could obtain it with dice rolls using our tool Dice2Seed, or we could obtain it with Electrum wallet, or with any other tool we think is the best for our needs.
Now we can store it in a text file, since we are assuming we are working in a live and offline environment, in most cases this should imply no risks. We can use this command to easily do that
echo 'your words here' > Documents/mnemonic
Now we can choose a file to hide our mnemonic seed in. In this case, we are using a copy of the AnuBitux wallpaper.
It is recommended to do this procedure on a copy of your files, to avoid corrupting or losing them if something goes wrong during the process.
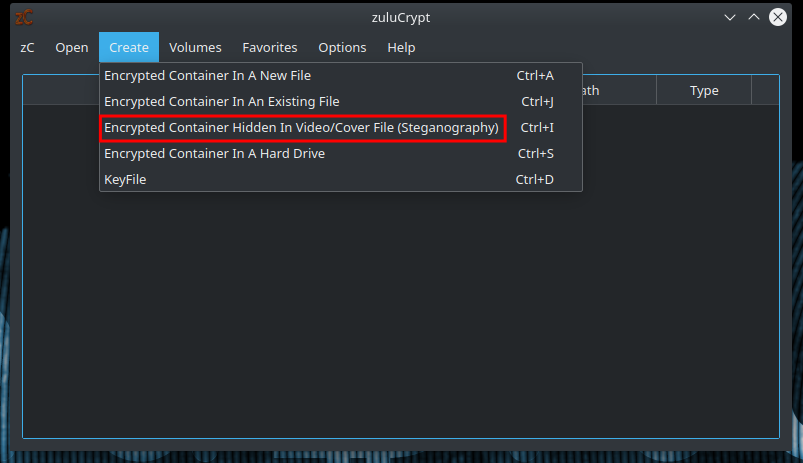
To hide our mnemonic, we are going to use ZuluCrypt. We can find its GUI in the AnuBitux encryption menu. The required feature, "Encrypted Container Hidden In Video/Cover File (Steganography)" can be found in the "Create" menu.
Clicking on it we have to provide the file we want to use to hide our information, a password to unlock it and the desired size.
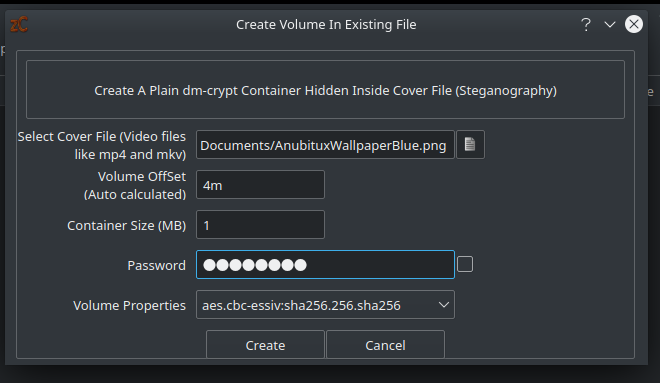
In this case, a size of 1 MB will be enough: if we are going to associate a big container with our picture, it would have a very big size that could look suspicious and attract undesired attention.
We also absolutely need to take care of the "Volume Offset" value, because we will need it every time we are going to unlock the container. It is calculated by the tool and indicates where it should look for the container to unlock.
Now we only have to click the "Create" button and our secret container is ready to be mounted. Before doing that, let's take a look at the size of the file we used to hide the container in.
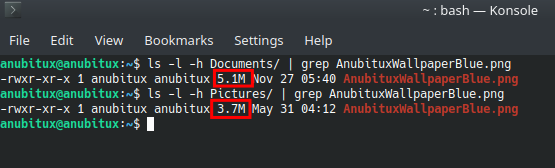
As we can see, the file we used for the procedure, even if it looks identical to the original one, has a bigger size of about 1.4 MB.
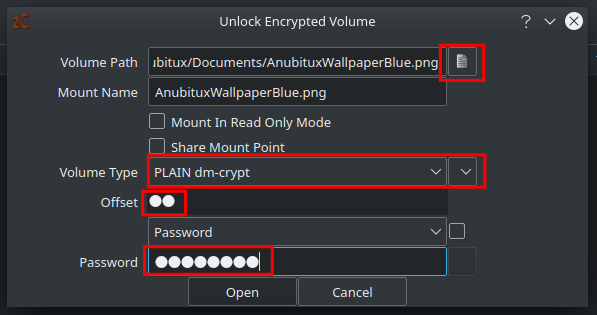
Now, let's access our container to store the mnemonic seed into it. We can do this with ZuluCrypt, using the "Volume Hosted In A File" feature under the "Open" menu.
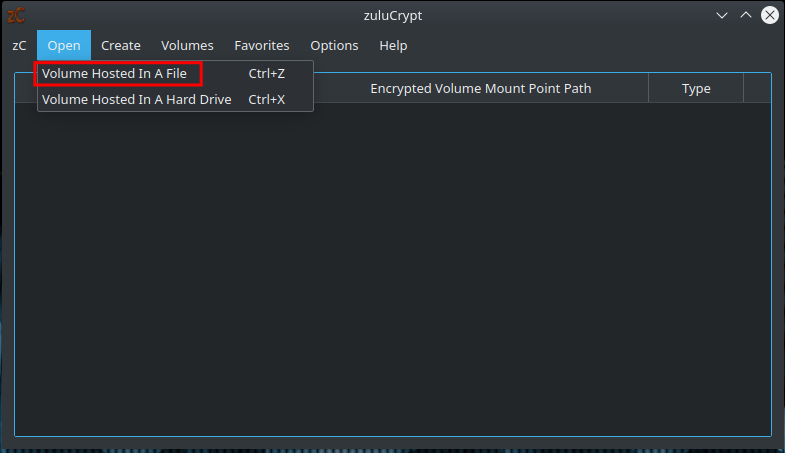
Now we have to:
- provide the file we used to hide the container;
- select "PLAIN dm-crypt" as "Volume Type";
- type the Offset value provided by the tool during the creation of the container;
- type the password we chose during the creation process;
- click on the "Open" button.
At this point, we can access the container with our file explorer.
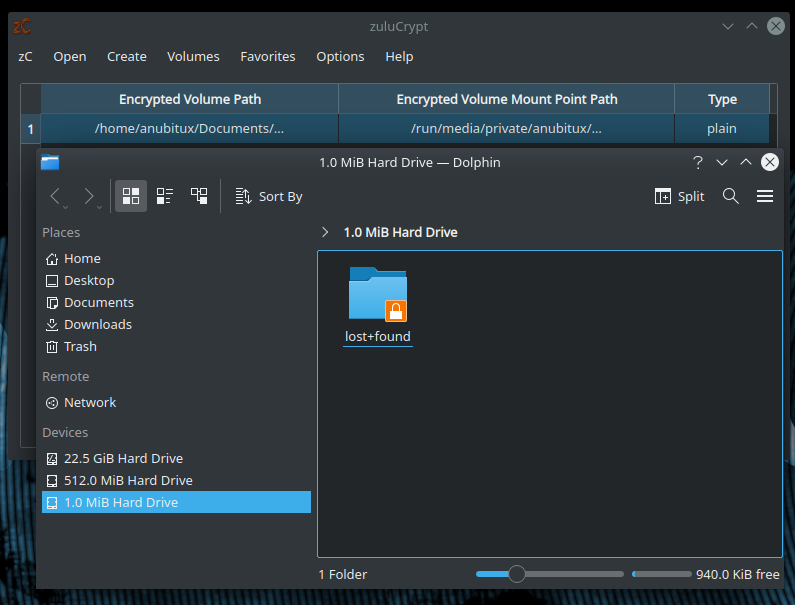
We are nor ready to copy our mnemonic seed to the container. Since we are working in a live environment, we do not need to delete it.
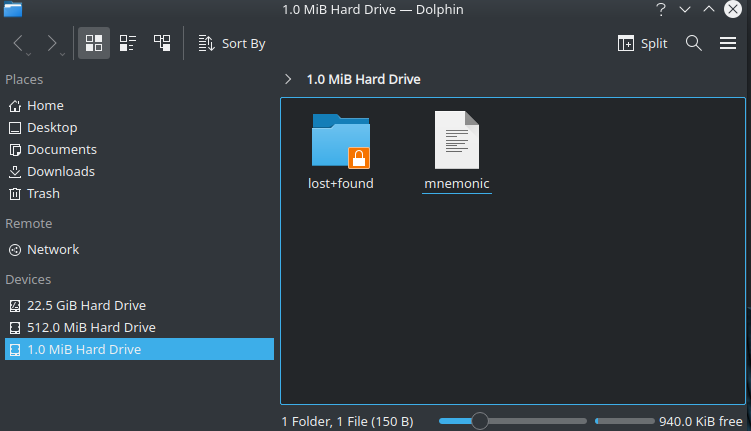
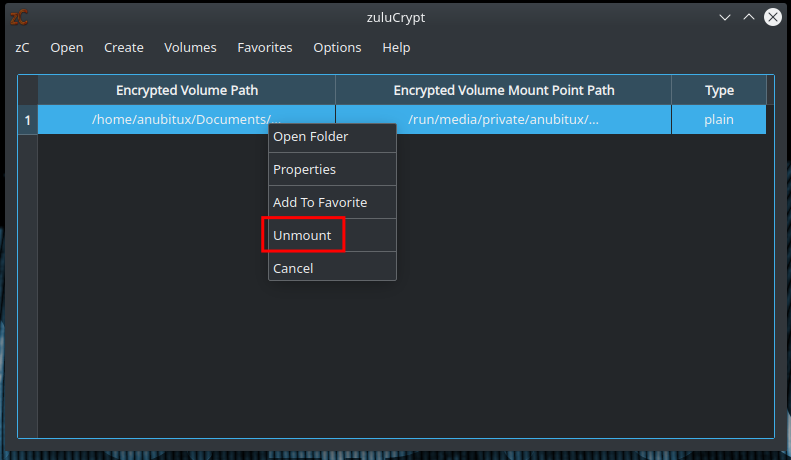
At this point we can unmount our volume, by right-clicking on it in the ZuluCrypt GUI and selecting the "Unmount" option.
How to store our container
We do not have to forget that we are working in a live environment and, if we shut down the system, our container will be irremediably lost. So, before shutting down our system, we should save it somewhere. We could put it on an encrypted drive or into another encrypted container we have previously created using VeraCrypt or some other similar solution.
Now, when we are sure our hidden container is in a safe place, we can shut down our system without connecting it to the Internet and also restarting it if we need to perform other operations.
Final thoughts
There could be infinite other solutions to safely store our mnemonic seed. This has not to be considered the best way to do this but only a suggestion on how to do that in a creative and secure way.
We also need to remember that more is the security we add to our information, the more it could be difficult for us to recover it if we lose or forget the right credentials.
It is also recommended to have more copies of the file hiding the container since the device we are storing it on could get broken or lost at any time and for many different unpredictable reasons.

